The data breach at Instructure’s Canvas learning platform is now the largest educational security incident ever recorded. But the full story is bigger and older than most coverage has let on. What started as a quiet API disruption on April 29 has turned into a live extortion campaign with ShinyHunters demanding payment by end of day tomorrow, May 12. Here is everything that has been confirmed, corrected and newly reported with sources for every claim.
What Happened – The Short Version
Instructure confirmed on May 1, 2026 that a criminal threat actor had gained unauthorised access to its systems. Investigators said ShinyHunters first accessed the systems on April 25, but the intrusion was not detected until April 29. The data exposure window ran from April 30 to May 7, lasting around eight days. The exposed data reportedly included names, email addresses, student ID numbers and private student-teacher messages. Instructure said it found no evidence that passwords, dates of birth, government IDs or financial information were accessed, but the investigation is still ongoing.
ShinyHunters claimed responsibility on May 3, issuing a “PAY OR LEAK” ransom threat. The group claimed it stole 3.65 TB of data from around 275 million users across nearly 9,000 institutions. TechCrunch reviewed sample data from two US schools and reported that a ShinyHunters member claimed the archive contained about 231 million unique email addresses though this figure was not independently verified.
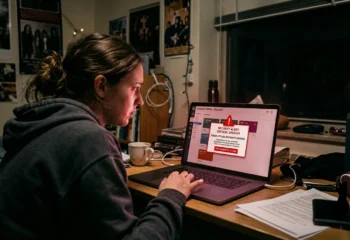
On May 7, Canvas was accessed again and students saw a new ransom note on their dashboards during final exam week. Instructure took Canvas offline and restored access on May 8. As of publication, the company had not confirmed whether it paid a ransom or what happened to the stolen data.
This Was Not a Surprise Attack
The May 2026 Canvas breach was not an isolated incident. ShinyHunters had been targeting Instructure’s environment for at least eight months before the attack. In September 2025, the group breached Instructure’s Salesforce business systems through social engineering. Instructure said no Canvas product data was affected and treated the incident as limited. However, security researchers now view it as an early warning that may not have been fully addressed.
Around the same period, ShinyHunters also targeted the University of Pennsylvania. After Penn refused to pay a $1 million ransom, the group published stolen university records on February 4, 2026, followed by another 461 MB of data on March 5. This gave Instructure at least eight months between the Salesforce compromise and the May 2026 Canvas breach to investigate and close possible access paths. The company has not publicly disclosed any major remediation during that period.
The “Containment” on May 2 Did Not Hold
Instructure’s public communications after the breach drew sharp criticism from security researchers. The company stated on May 2 that the incident had been “contained.” Its CISO, Steve Proud, said the company had revoked the attacker’s access, rotated API keys and deployed patches.
Five days later, ShinyHunters was back inside. The group’s ransom note on May 7 stated bluntly, “Instead of contacting us to resolve it, they ignored us and did some ‘security patches.'”
Instructure also appeared to obscure the second breach from users in real time. On May 7, students began seeing the ShinyHunters ransom note on Canvas login pages The Daily Pennsylvanian reported the ransom note was replaced at approximately 4:20 p.m. Eastern on Penn’s login page specifically, Wikipedia and other platform-wide sources record Instructure’s maintenance message appearing at approximately 8 p.m. Eastern across Canvas broadly. The platform-wide timing of 8 p.m. is the more widely corroborated figure. The precise gap between the defacement and Instructure’s public acknowledgement remains disputed and has not been independently corroborated. Krebs on Security reported on the incident but the specific 21-minute figure has not been confirmed.
The Root Cause: Free-For-Teacher Accounts
Instructure confirmed that the attacker exploited a weakness in its Free-For-Teacher account program. This program let educators create Canvas accounts without institutional verification, giving them access to Canvas features for classroom use. Because these accounts were active production Canvas tenants with lighter security requirements, they provided an entry point into institutional data that would not have been possible through normal verified accounts.
Instructure permanently shut down the Free-For-Teacher program on May 7. The confirmed exposure window ran from April 30 to May 7, 2026 approximately eight days. The company detected the intrusion roughly one day after the window opened.
Who Was Affected, The Global Scope
The breach had a global impact affecting educational institutions in at least nine countries including the US, Canada, UK, Australia, Sweden, the Netherlands, New Zealand, Singapore and Hong Kong. In the US, Canvas is widely used across higher education and K-12 schools, meaning some affected users may be minors. Australia reported major disruption across schools and universities.
In Sweden, 31 universities were affected including Försvarshögskolan, the Swedish Defence University, which trains military officers and defence personnel. The university said it is treating itself as compromised under the precautionary principle and has reported the breach to Sweden’s Data Protection Authority, IMY. Canada, the Netherlands, Hong Kong and New Zealand also reported affected universities, colleges and schools with some institutions suspending or disconnecting Canvas from internal systems while investigations continue.
How ShinyHunters Operates
ShinyHunters typically relies on cloud misconfigurations, stolen OAuth tokens, API credentials and social engineering rather than advanced malware or zero-day exploits. Its recent campaigns show a shift towards vendor ecosystems, targeting platforms that connect thousands of organizations at once.
The group’s extortion model is simple. Steal data, name the victim publicly, set a deadline and threaten publication. In the Instructure case, ShinyHunters escalated pressure after the May 6 deadline by reportedly defacing Canvas login pages at around 330 institutions and contacting the media directly.
The group has set a final deadline for the end of May 12, 2026. Instructure has not confirmed whether it paid a ransom or secured the stolen data. If the data is leaked, names, email addresses, student IDs and private messages could be used for phishing, identity fraud and social engineering.
What You Should Do Right Now
Regardless of whether a ransom is paid, the data that was accessed is already in ShinyHunters’ possession. Anyone who has used Canvas at any point since approximately 2020 should treat their data as potentially exposed.
- Change your Canvas password immediately, even if your institution has not yet notified you.
- If you reused that password anywhere else, change it on those services too.
- Be highly sceptical of any email, message or call claiming to be from your school, Canvas or Instructure, especially ones asking for login credentials or payment details.
- For parents of school-age children, the breach may include your child’s name, school email and student ID. Watch for targeted communications directed at them.
- For institutions using Canvas integrations via API, audit which third-party applications have active access and revoke anything not currently necessary.
- Maintain elevated phishing awareness for at least 90 days. ShinyHunters have used stolen data for targeted follow-on campaigns well after the original breach in past incidents.
References
- Canvas Breach Disrupts Schools & Colleges Nationwide
- Hackers steal students’ data during breach at education tech giant Instructure
- Hackers deface school login pages after claiming another Instructure hack
- ShinyHunters Claims Second Attack Against Instructure
- Education Sector in the Crosshairs: ShinyHunters’ Extortion Campaign Against Instructure
- Penn data leaked after University refused to pay $1 million ransom
- Cybercrime group crashes Penn’s Canvas system, demands ransom
- Säkerhetsincident i lärplattformen Canvas
- Technical Advisory: ShinyHunters Breach of Instructure Canvas LMS
This post is also available in:
Svenska